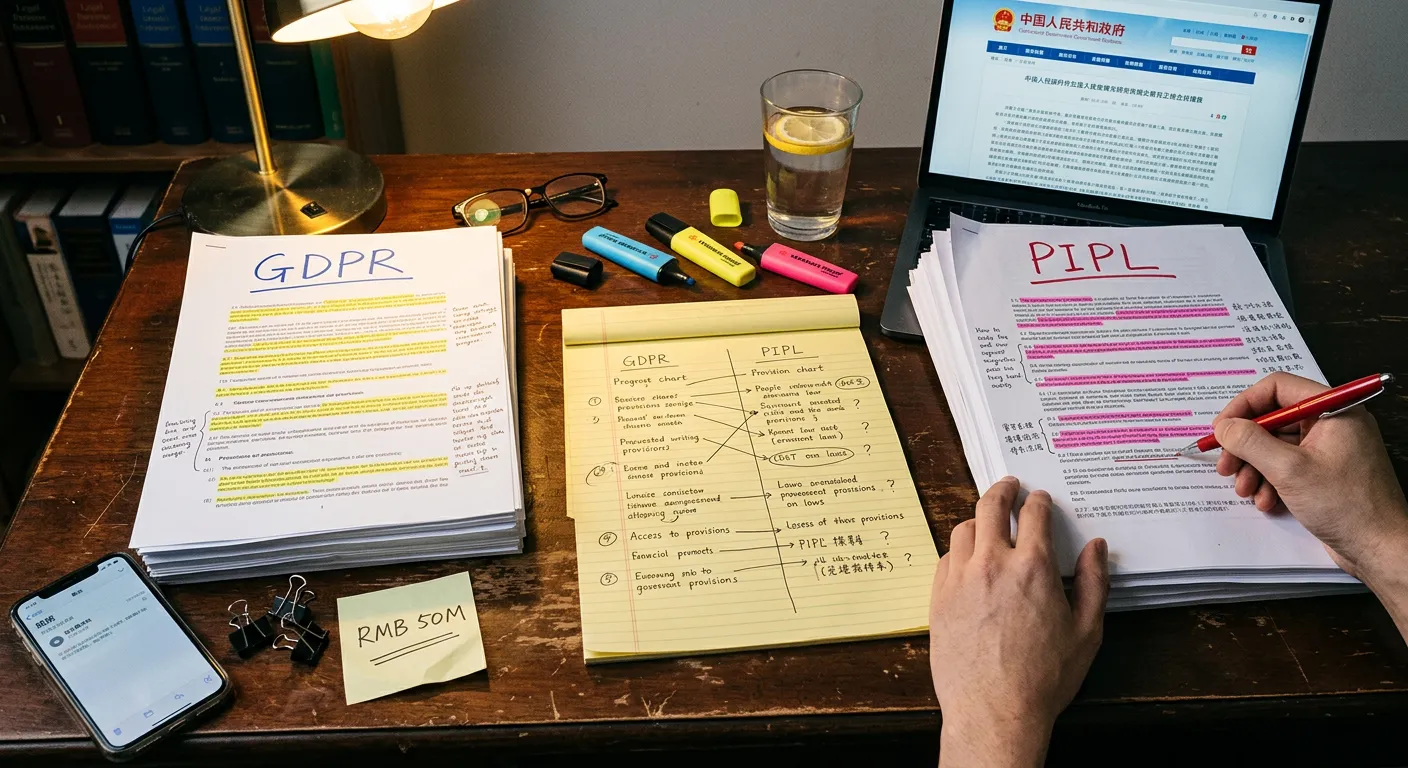
Most foreign companies assume China’s data privacy laws only kick in if you have an office in Beijing or Shanghai. That’s not how it works. The PIPL - China’s answer to GDPR - applies to any entity processing personal information of Chinese residents, no matter where that entity is located. If your website uses cookies, collects emails, or tracks user behaviour for visitors from China, you’re in scope. Penalties for serious violations run up to RMB 50 million or 5% of your prior year’s turnover. Compliance audits became mandatory in May 2025. This is not a future concern. It’s happening now.
Three Laws at a Glance
| PIPL | Data Security Law | Cybersecurity Law | |
|---|---|---|---|
| Effective | November 2021 | September 2021 | June 2017 |
| Scope | Personal information of Chinese residents | All data processed in China | Network operations in China |
| Applies to foreign companies outside China? | Yes | Only with China operations | Only with China operations |
| Cross-border transfers | Security assessment, contracts, or certification | Restrictions on important data | Security assessment required |
| Key penalty | Up to RMB 50M or 5% of turnover | Fines + possible shutdown | Fines + licence revocation |
| Mandatory audits | Yes (since May 2025) | Classification required | Security assessments |
PIPL: The Law That Follows You Home
The Personal Information Protection Law took effect in November 2021 and is the one foreign companies need to understand first. Unlike the other two laws in China’s framework, PIPL reaches across borders. It applies to any entity anywhere in the world that processes personal information of people in China.
What that looks like in practice: if your website serves Chinese users and collects anything - names, email addresses, phone numbers, browsing behaviour, device IDs - PIPL applies to you. Doesn’t matter if you’re based in Shanghai, San Francisco, or Stockholm. Doesn’t matter if you’ve never set foot in China. If the data belongs to Chinese residents, the law applies.
PIPL has extraterritorial reach. If you process personal data of Chinese residents, the law applies to you regardless of where your company is located.
Compliance audits became mandatory in May 2025. If you’re processing data on more than 1 million individuals, you need a Data Protection Officer. Cross-border data transfers, meaning anytime Chinese user data leaves the country, require either a government security assessment, standard contractual clauses, or certification through an approved body. You can’t just pipe data back to your servers in Frankfurt and call it a day.
Penalties: up to RMB 50 million or 5% of prior year’s revenue, whichever is higher. Individual executives can be held personally liable too. If you’ve been through GDPR compliance, the structure will feel familiar and the penalties are in the same ballpark.
Penalties for serious PIPL violations: up to RMB 50 million or 5% of prior year’s turnover. Individual executives can also be held personally liable.
DSL and Cybersecurity Law: The Other Two Pillars
The Data Security Law (September 2021) and the Cybersecurity Law (June 2017) round out the framework. They matter most to companies with operations or data processing physically located in China.
The DSL covers all data processing within China, not just personal data. It sorts data into three tiers: core state data, important data, and general data. Companies need to build classification systems and apply protection measures that match each category. Transferring important data across borders faces additional restrictions and may need government sign-off.
The Cybersecurity Law is the oldest of the three. It requires network operators to store data generated in China on Chinese servers. Operators of critical information infrastructure get hit with tighter rules: mandatory security assessments, enhanced protocols, stricter reporting.
For most foreign companies running a website aimed at Chinese users, PIPL is what you need to worry about first. The DSL and Cybersecurity Law become more directly relevant once you have servers, staff, or data operations on the ground in mainland China.
What Foreign Companies Actually Need to Do
If your company collects or processes data from Chinese users in any form, this isn’t a nice-to-have checklist.
| Requirement | Details |
|---|---|
| Data Protection Officer | Required if processing data of 1M+ individuals |
| Data classification | Map what you collect to DSL categories |
| Data storage | Chinese user data on servers in mainland China |
| Explicit consent | Active, informed user consent before collection |
| Cross-border assessment | Government assessment, contracts, or certification |
| Compliance audits | Mandatory under PIPL since May 2025 |
| Breach notification | Procedures must be in place before a breach occurs |
Appoint a DPO. If you’re processing data on more than 1 million individuals, you need a Data Protection Officer. PIPL requirement. Not a recommendation.
Classify your data and figure out what you’re collecting, how sensitive it is, and how it maps to DSL categories. Core state data and important data carry heavier obligations.
Store Chinese user data in China. Personal data from Chinese users needs to live on servers physically located in mainland China. Required by the Cybersecurity Law, reinforced by PIPL.
Get real consent. Before collecting personal information you need explicit, informed consent. Not a pre-checked checkbox. Not terms buried in a footer nobody reads. Actual consent that the user actively provides.
Explicit consent means the user actively agrees. Pre-checked boxes and implied consent through continued browsing don’t meet the PIPL standard.
This trips up a lot of companies that are used to the “by continuing to use this site you agree” approach.
Handle cross-border transfers properly. If Chinese user data needs to leave China - flowing to your company servers in Europe or the US, for example - you have to go through a government security assessment, standard contracts, or certification. There is no shortcut and no exception for small volumes.
Run compliance audits. Mandatory under PIPL since May 2025. Not a one-time thing. Ongoing, and auditors are paying attention.
Have breach procedures ready before you need them. Data breach happens, you’re required to notify authorities and affected individuals within mandated timeframes. Companies that figure out their notification process after a breach has already occurred are in a much worse position.
Need help with this?
ChinaWebFoundry handles WordPress projects in China end to end. If any of this feels like more than you want to tackle alone, get in touch.
Talk to Us